A Guide to Regulatory Compliant Healthcare Software Development
When you’re building health tech, regulatory compliant healthcare software development isn’t just a box to tick; it’s the very ground you build on. It’s about consciously designing medical software to meet strict legal and safety rules like HIPAA in the US and GDPR in Europe. This protects patients, ensures your software works as intended, and frankly, keeps your business viable.
Thinking about compliance from day one, or ‘compliance-by-design’, might seem like a hurdle. But in reality, it’s what turns a potential liability into a core business strength, building the trust you need to succeed and stay in the market.
The High Stakes of Healthcare Software Compliance

In health tech, the “move fast and break things” mantra is a recipe for disaster. The stakes couldn’t be higher. Regulators are watching more closely than ever, and they aren’t afraid to hand out severe penalties for getting it wrong. Compliance isn’t a final check before launch; it’s central to responsible innovation.
The financial fallout alone is enough to get your attention. In fiscal year 2025, the U.S. Department of Justice reported a staggering $6.8 billion in False Claims Act settlements. Of that, nearly $5.7 billion came directly from the healthcare industry. These aren’t just numbers; they represent a global crackdown and underscore the enormous financial risks of cutting corners.
Beyond Fines to Fundamental Trust
While massive penalties make the news, the real damage from a compliance failure goes much deeper. It can corrode a company from the inside out.
-
Irreparable Brand Damage: It takes years to build trust with patients, but only one data breach to destroy it. That trust is your most valuable asset.
-
Operational Disruption: Nothing brings a business to a halt like a regulatory audit or legal battle. They drain resources, freeze development, and can paralyze your entire operation.
-
Loss of Market Access: If you don’t meet the standards set by bodies like the FDA, you can be locked out of key markets, stopping your growth dead in its tracks.
Solid internal policies are your first line of defense. For instance, clear conflict of interest policy examples for healthcare are crucial for managing internal risks and protecting the integrity of your software. Good governance is the bedrock of any lasting compliance strategy.
Shifting from Reactive to Proactive Compliance
The only sustainable way forward is to bake compliance into your strategy from the very beginning. It has to be proactive. This means weaving regulatory considerations into every phase of your development lifecycle, from the first napkin sketch to long-term maintenance after launch.
For many teams, this shift requires a new mindset and often, expert guidance to truly implement a ‘compliance-by-design’ model.
When you take this approach, every feature you build and every line of code you write rests on a solid foundation of security and privacy. Suddenly, compliance isn’t a burden you have to carry. It becomes a powerful differentiator that signals your absolute commitment to safety, earning you the trust of patients, providers, and partners alike.
Navigating the world of healthcare software can feel like trying to read a map in a dozen different languages at once. You’ve got a jumble of acronyms: HIPAA, GDPR, FDA, MDR, and each one represents a non-negotiable set of rules you have to follow. Getting this right isn’t just about avoiding fines; it’s about building trust and ensuring patient safety.
Let’s break down this regulatory landscape. Think of these rules not as obstacles, but as different sets of architectural plans for building a hospital. One set of plans (like HIPAA) details how to secure patient rooms and records. Another (like FDA rules) specifies how to build and test the life-support machines. They all serve a common goal: a safe, functional, and trustworthy environment.
Before we dive into the specifics of each regulation, it’s helpful to see how they compare at a high level. Each has a different geographic reach and a unique primary focus, from data privacy to medical device safety.
Key Healthcare Regulations at a Glance
| Regulation/Standard | Geographic Scope | Primary Focus | Key Requirement Example |
|---|---|---|---|
| HIPAA | United States | Protecting patient health information (PHI) | Implementing administrative, physical, and technical safeguards for electronic PHI. |
| GDPR | European Union | Protecting the personal data and privacy of EU citizens | Granting individuals the “right to be forgotten” (data erasure). |
| FDA (e.g., SaMD) | United States | Safety and effectiveness of medical devices, including software | Formal validation and verification to prove the software works as intended. |
| MDR/IVDR | European Union | Safety and performance of medical devices and in-vitro diagnostic devices | Establishing a comprehensive Quality Management System (QMS). |
| ISO 13485 | International | Quality Management Systems for medical devices | Documenting every stage of the device lifecycle, from design to post-market surveillance. |
This table gives you a quick snapshot, but the real challenge lies in understanding how these rules apply to your day-to-day development work. Let’s look closer at the heavy hitters.
HIPAA: The US Standard for Health Data Privacy
In the United States, everything starts with the Health Insurance Portability and Accountability Act (HIPAA). It’s the bedrock law for protecting patient privacy and governs how any Protected Health Information (PHI) is handled. HIPAA isn’t a single rule but a family of them.
-
The Privacy Rule: This is all about who gets to see and share patient data. It establishes the fundamental principle that information should only be used for healthcare operations, treatment, and payment, unless a patient gives explicit consent for other uses.
-
The Security Rule: This part is for us in tech. It gets specific about how to protect electronic PHI (ePHI), mandating a mix of administrative (risk assessments, training), physical (server room locks, screen privacy), and technical (encryption, access controls) safeguards.
-
The Breach Notification Rule: If something goes wrong and data is compromised, this rule kicks in. It requires you to notify affected patients and the government, making transparency a legal requirement.
As we explored in our guide, you can cover the practical steps for weaving these rules into your workflow in our detailed look at HIPAA-compliant application development.
GDPR: Europe’s Take on Fundamental Data Rights
While HIPAA is US-centric, the General Data Protection Regulation (GDPR) from the European Union has a long reach. If your software handles the personal data of anyone in the EU, even if your company is based in California, you need to comply.
GDPR fundamentally shifts the power dynamic. The individual owns their data, not the company collecting it. This translates into powerful user rights, like the right to access, correct, and even erase their data (the “right to be forgotten”). For developers, this means you must build systems with consent at their core and have clear processes for exporting or deleting user data on demand.
A guiding principle shared by both HIPAA and GDPR is data minimization. Only collect what you absolutely need for a clearly defined purpose. If you don’t need a user’s date of birth to provide your service, don’t ask for it. This simple habit drastically shrinks your security risk and compliance burden.
FDA and SaMD: When Your Software Becomes a Medical Device
The moment your software is used to diagnose, treat, or prevent a disease, you’ve likely crossed a critical threshold. It’s no longer just a health app; it’s potentially a medical device, and that brings regulators like the U.S. Food and Drug Administration (FDA) to your doorstep.
-
Software as a Medical Device (SaMD): This is a formal classification for software that performs a medical function on its own, like an application that analyzes MRI scans for signs of a tumor. The FDA requires rigorous proof that the software is both safe and effective, which involves extensive documentation and clinical validation.
-
21 CFR Part 11: This specific regulation sets the rules for electronic records and signatures. It ensures that digital records are just as trustworthy and legally binding as paper ones, a crucial requirement for any system that replaces traditional paperwork, like an Electronic Health Record (EHR).
-
ISO 13485: This isn’t a law, but an international standard for a Quality Management System (QMS) for medical devices. Adopting it is often the most direct path to complying with FDA and EU regulations. It provides a complete framework for ensuring quality is baked into every single step, from the first line of code to post-launch monitoring.
Weaving Compliance into Your Development Lifecycle
Trying to bolt on compliance at the end of a project is a surefire way to invite delays, budget overruns, and serious regulatory trouble. Think of it this way: you wouldn’t build a house and then try to figure out where the plumbing goes. That’s a recipe for disaster.
Truly effective healthcare software development embeds compliance from the very beginning. It’s not about passing a single audit; it’s about building safety and privacy into the DNA of your product. This “Compliance-by-Design” approach transforms regulatory hurdles into a framework for creating higher-quality, more secure software from the ground up. By weaving controls and documentation into every phase, you create a clear, auditable trail that demonstrates your commitment to patient safety right from the start.
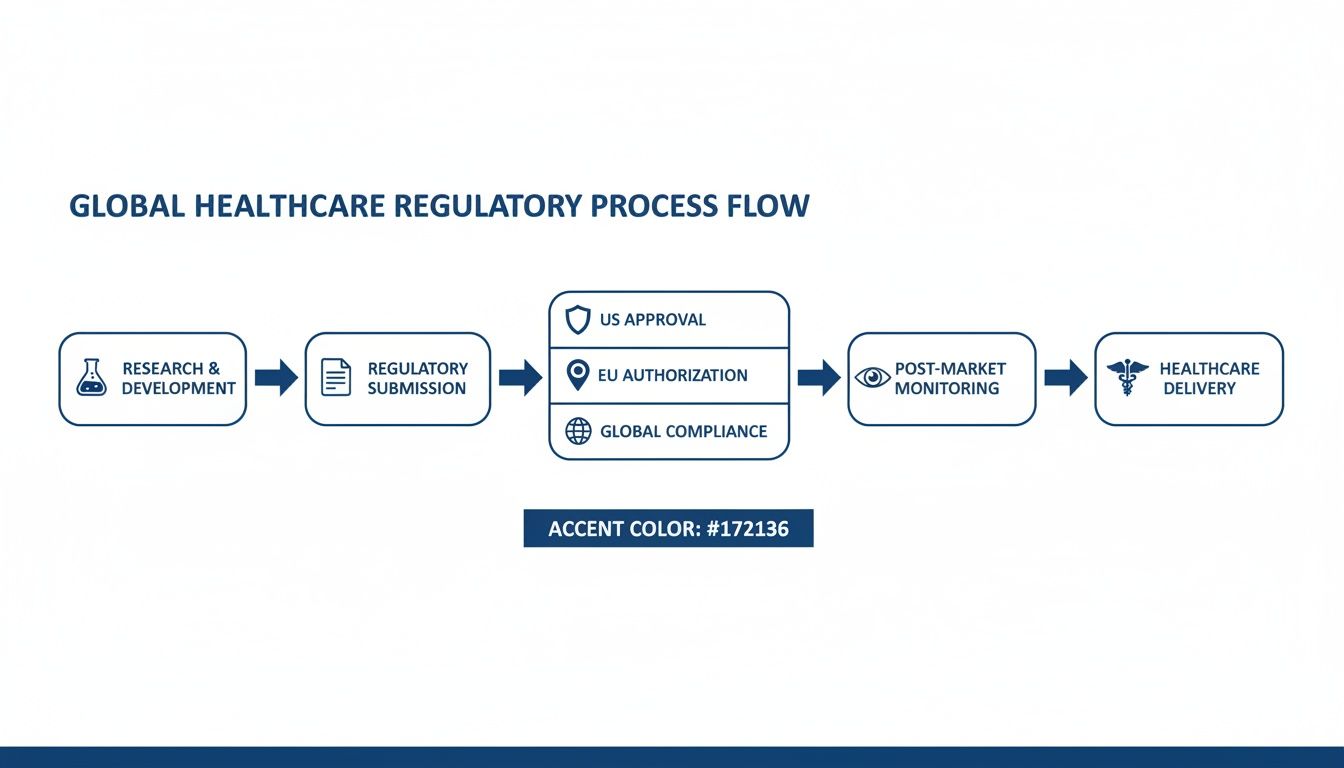
As you can see, compliance isn’t a single gate you pass through. It’s a continuous cycle where rules like HIPAA in the US, GDPR in the EU, and other global standards influence every decision you make, from initial idea to long-term maintenance.
Phase 1: Discovery and Requirements
This is your foundation. Before a single line of code gets written, you have to map out every regulation and standard that applies to your project. Get this wrong, and you’ll be building on sand.
Here’s what needs to happen:
-
Regulatory Requirements Specification (RRS): This isn’t just a list of rules. It’s where you translate dense legal text from regulations like HIPAA or GDPR into specific, actionable software requirements. For instance, GDPR’s “right to be forgotten” becomes a technical spec for a feature that can surgically and permanently remove a user’s data from every system and backup.
-
Privacy Impact Assessment (PIA): Think of this as a pre-mortem for privacy. It forces you to ask tough questions about the Protected Health Information (PHI) you plan to handle. What data are we collecting? Do we absolutely need it? How will we protect it at every step?
-
Risk Analysis (ISO 14971): For anything classified as a medical device, this is a non-negotiable. It’s a formal process for identifying potential hazards, figuring out how likely they are to happen, and defining concrete controls to prevent them. It’s all about answering: “What’s the worst that could happen, and what’s our plan to stop it?”
Phase 2: Design and Architecture
With your requirements clearly defined, you can now design a system that’s inherently secure and compliant. The architectural choices made here will either be a constant headache or a powerful asset for years to come.
A guiding principle here is data minimization. Your system should be architected to collect, process, and store the absolute minimum amount of data required to function. The less data you hold, the smaller your risk and compliance footprint.
Key design activities include:
-
Threat Modeling: This is a structured brainstorming session where you try to “break” your own system. You imagine potential security threats, like a bad actor trying to access patient records, and then design specific countermeasures, such as mandatory multi-factor authentication and strict role-based access controls.
-
Architecting for Security: This means security isn’t a feature you add later. It’s part of the core blueprint. Things like encryption (for data in transit and at rest), secure data storage protocols, and robust identity management are designed into the system from day one.
Phase 3: Development and Implementation
This is where the rubber meets the road, as your development team turns the secure design into clean, functional code. Discipline and adherence to standards are everything in this phase.
A focused approach is critical:
-
Secure Coding Practices: Developers must live and breathe standards like the OWASP Top 10. This helps prevent common but dangerous vulnerabilities, such as SQL injection attacks or broken access controls that could expose sensitive data.
-
Robust Access Controls: The code itself must enforce the principle of least privilege. This means a user can only access the specific data and features essential for their job. A physician needs to see clinical records, but a billing administrator should be firewalled off from everything but the necessary financial data.
For a much deeper look at these practices, our guide on the Secure Software Development Lifecycle is a great resource.
Phase 4: Testing and Validation
Now you have to prove it. This phase is all about producing evidence that you not only built the software correctly but also that you built the right software. This involves two distinct but critical activities: verification and validation.
-
Verification: This answers the question, “Did we build the software right?” It involves unit tests, integration tests, and meticulous code reviews to confirm the software works according to its technical specifications.
-
Validation: This answers a more important question: “Did we build the right software?” It confirms the product actually meets the user’s needs and its intended use, a crucial step for gaining regulatory clearance from bodies like the FDA.
Testing activities must include a formal Validation Plan, a battery of test cases that trace directly back to the initial requirements, and aggressive penetration testing to uncover vulnerabilities that standard QA might miss.
Phase 5: Deployment and Maintenance
Your work on compliance is never truly done. Once the software is live, it becomes an ongoing operational responsibility. New threats emerge, and regulations are constantly updated.
Your post-launch strategy must be built for the long haul:
-
Continuous Monitoring: You need to be actively watching your systems for any suspicious activity, security vulnerabilities, or performance degradation.
-
Incident Response Plan: Have a documented and rehearsed plan for what to do when, not if, a security incident or data breach occurs.
-
Change Management: Implement a formal process for documenting, testing, and approving any software changes. This ensures that a simple update doesn’t accidentally open up a new compliance gap or security risk.
Navigating AI Compliance in Healthcare Software

There’s no denying the excitement around artificial intelligence in medicine; it’s helping to personalize treatments, sharpen diagnostics, and streamline hospital operations. But as soon as you bring AI into the picture, you’re also introducing a whole new layer of compliance challenges. The unique way AI functions creates risks that your standard software development rulebook simply wasn’t designed to handle.
The biggest worries revolve around things like algorithmic bias, the infamous “black box” problem, where no one can explain how the AI reached its conclusion, and the sheer volume of data needed to train these models. It’s a real and valid concern. For example, if your diagnostic AI was trained primarily on data from one demographic, it could easily make dangerous errors when used with others, leading to poor patient outcomes and massive legal exposure.
This isn’t just speculation; it’s a major point of anxiety for industry leaders. A recent survey of over 550 payer executives found that 53% are worried about data privacy risks from AI, and 52% are concerned about the accuracy of its outputs. This paints a clear picture of the tightrope walk that is regulatory-compliant healthcare software development when AI is involved. As the full report on balancing cost and compliance in a disruptive era shows, many organizations know they have big gaps in their current compliance strategies.
AI: The Problem and The Solution
Here’s the interesting twist: AI isn’t just the source of new regulatory headaches; it’s also one of the most powerful tools we have to solve them. When applied correctly, AI can become your best compliance ally, automating and reinforcing the very controls you need to keep your systems secure and auditable.
Instead of seeing AI as just another liability to manage, it’s more productive to view it as a capability. The trick is to get ahead of its risks while putting its strengths to work for you. Understanding how to use AI for your business is key.
The goal isn’t to shy away from AI but to master its responsible implementation. By turning AI’s own analytical power back onto itself and the systems it runs on, you build something that isn’t just compliant; it’s smarter, safer, and more resilient. You can turn a potential vulnerability into a core competitive advantage.
How to Tackle Algorithmic Risks in Health Tech
Dealing with the unique risks of AI requires a specific, proactive strategy. You can’t just bolt on some extra QA at the end of the development cycle. You need to build fairness, transparency, and security into the DNA of your AI models from day one.
Key Mitigation Strategies:
-
Bias Audits and Fairness Toolkits: Before you even think about deploying a model, it needs to be rigorously stress-tested for bias. This means running it against different demographic datasets to prove its predictions are fair and equitable for everyone.
-
De-identified and Anonymized Data: This is a big one. Whenever you can, use de-identified or even synthetic data for model training. It dramatically lowers the privacy risks that come with handling huge amounts of Protected Health Information (PHI).
-
Explainable AI (XAI) Techniques: The “black box” is a non-starter for regulators and clinicians. Using XAI methods like LIME or SHAP peels back the layers, making the AI’s decision-making process transparent. This is critical for understanding why a model made a certain recommendation. As we explored in our guide, you can learn more about this in our article on responsible AI engineering.
Putting AI on Your Compliance Team
Beyond just managing its own risks, AI can be put to work enforcing compliance across your entire technology stack. This is where the technology moves from being a potential problem to an essential part of the solution.
Expert AI development services can help you build systems that use machine learning for sophisticated compliance monitoring. A well-structured AI transformation framework can weave these capabilities directly into your daily operations.
How AI Can Power Your Compliance Efforts:
-
Predictive Risk Analytics: Think of this as a digital early-warning system. AI algorithms can analyze system logs, network traffic, and user behavior to spot patterns that signal a potential data breach or compliance violation before it actually happens.
-
Automated Audit Logging: Manual audit trails are prone to error and gaps. An AI can automatically and meticulously log every single time-sensitive data point accessed, creating a perfect, unchangeable record that will make auditors happy.
-
Real-Time Anomaly Detection: A machine learning model can quickly learn what “normal” activity looks like on your network. The moment something deviates from that baseline, like a user suddenly trying to download thousands of patient records at 3 AM, the AI can flag it instantly.
By embracing both sides of the AI coin: managing its risks with diligence while deploying its strengths with strategy, you can create next-generation healthcare software that is not only innovative but fundamentally safe, secure, and compliant.
Mastering Documentation for Audit Readiness
There’s a simple, unshakeable rule in regulated health tech: if it wasn’t documented, it didn’t happen. From an auditor’s point of view, your code, no matter how brilliant, is just a claim. Your documentation is the proof.
This paper trail isn’t about ticking boxes. It’s the story of your product, showing that every single decision was deliberate and made with patient safety and compliance front and center. Without a clear and traceable record, even the most innovative software will fail scrutiny. This is why properly documenting IT processes is less of a task and more of a foundational discipline for any team in this space.
Building Your Audit-Ready Story
Your documentation should tell a cohesive story. Three core documents act as the central pillars of this narrative: the Software Requirements Specification (SRS), the Risk Management File, and the Verification and Validation (V&V) Plan.
-
Software Requirements Specification (SRS): Think of this as the master blueprint. It goes way beyond a simple feature list. It must capture every single functional, technical, and regulatory requirement the software is expected to meet. Each requirement needs a unique ID so you can trace it from concept to code to final testing.
-
Risk Management File (ISO 14971): This is your evidence of proactive risk mitigation. It’s where you document every potential hazard, analyze how likely and severe it is, and then detail the exact controls you built to prevent it from causing harm. This file directly answers an auditor’s most pressing question: “How did you make sure this software is safe?”
-
Verification and Validation (V&V) Plan: This document lays out your entire testing strategy. It specifies the methods, tools, and pass/fail criteria you’ll use to prove two things: that the software was built correctly and that it actually does what it’s supposed to do.
The real magic happens when these documents are interconnected. A requirement in the SRS leads to a risk assessment in the Risk Management File, which is then confirmed by a specific test case in the V&V plan. That creates the unbroken chain of evidence auditors need to see.
Verification vs. Validation: A Critical Difference
It’s easy to mix up verification and validation, but they answer two very different and equally critical questions. Getting this wrong is a classic mistake that leaves major gaps in your compliance evidence.
Verification asks: “Did we build the software right?”
This is an internal, technical check. It confirms that the software was built according to its own design and specifications.
Verification activities usually include:
-
Code reviews
-
Unit tests and integration tests
-
Static code analysis
Basically, verification is about making sure the code is clean and functions exactly as the developers intended.
Validation asks: “Did we build the right software?”
This is an external, user-focused process. It confirms the software meets the real-world needs of its users and accomplishes its intended purpose safely and effectively.
Validation activities often involve:
-
Usability testing with actual clinicians or patients
-
Clinical simulations or trials
-
User Acceptance Testing (UAT)
Here’s a simple analogy: think of building a house. Verification is checking that the wiring is up to code and the plumbing doesn’t leak. Validation is having the family move in to confirm the layout works for their lifestyle and the house truly feels like a home.
Pulling all this documentation together is a serious undertaking. A dedicated development team with a background in regulated software can help turn this requirement from a burden into a powerful quality framework, ensuring you’re always ready for an audit.
Future-Proofing Your Health Tech Against Regulatory Change
If there’s one constant in health tech, it’s that the rulebook is always changing. The compliance standards that work today could easily become obsolete tomorrow. We’re seeing this happen in real-time as telehealth explodes, medical IoT devices become commonplace, and AI-driven diagnostics force regulators to constantly play catch-up.
Simply reacting to these changes after the fact is a losing game. The only sustainable strategy is to build a platform that is designed for adaptation from the ground up. This means leaving behind static, manual compliance checklists and embracing automated, continuous monitoring that can keep pace with evolving regulations. Honestly, this is where choosing the right technology partner can make or break your product.
Embracing Automated and Continuous Compliance
The move from ticking boxes on a spreadsheet to implementing automated compliance isn’t just a nice-to-have; it’s quickly becoming a necessity for survival. You just have to look at the numbers. The market for healthcare compliance software is predicted to jump from USD 4.37 billion in 2026 to a staggering USD 7.51 billion by 2031.
This isn’t happening in a vacuum. The surge is a direct response to the escalating risk of data breaches and much stricter enforcement. In 2024 alone, breaches have already exposed 133 million patient records. This has led to USD 28.3 million in penalties, including one particularly painful USD 4.75 million HIPAA settlement for a company with inadequate risk assessments. The folks at Mordor Intelligence have some great insights on this market shift if you want to dig deeper.
Automating compliance gives your system a nervous system: it can detect, alert, and respond to potential issues as they happen, not weeks or months later during a manual audit. This is the very core of building a future-proof platform.
Strategies for Building a Resilient Platform
A truly resilient platform is the result of smart architectural decisions and a forward-thinking development culture. It’s not just about following today’s rules; it’s about building a system that can absorb tomorrow’s requirements without a complete overhaul. A good healthtech software development partner can help you embed this thinking right into your product’s DNA.
Here are a few key strategies we’ve seen work time and time again:
-
Modular Architecture: Think of your software as a set of LEGO bricks instead of a single, solid block. By designing it in independent, swappable modules, you can update a specific function to meet a new regulation without tearing the whole thing down.
-
API-First Design: When you build your system around a clean, well-documented API, you make it far easier to integrate new tools, data sources, and services as the health tech ecosystem evolves.
-
Proactive Regulatory Intelligence: Don’t wait for rule changes to hit the news. Actively keep an eye on what regulatory bodies like the FDA and global data protection authorities are discussing. This lets you see what’s coming down the pike and adjust your roadmap before it becomes a crisis.
A forward-thinking approach transforms compliance from a reactive scramble into a proactive strategy. By embracing custom healthcare software development, you’re not just building for today’s market; you are creating a resilient platform poised to capture the opportunities of 2026 and beyond.
Our own client cases show how this focus on future-readiness pays off, resulting in secure, adaptable systems that truly stand the test of time.
Frequently Asked Questions (FAQ)
When you’re building healthcare software, a lot of questions come up around the complex web of regulations. Let’s walk through a few of the most common ones we hear from our clients.
Where do we even start with compliance for a new health app?
Before a single line of code gets written, your first move is a Regulatory and Privacy Impact Assessment. Think of this as creating a compliance blueprint during your discovery phase. It’s all about identifying exactly which rules, like HIPAA in the U.S. or GDPR in Europe, apply to your software based on what it does, who will use it, and the type of data it handles.
Once you have that map, the next step is to partner with a team that specializes in custom software development to draft a detailed Regulatory Requirements Specification. This document becomes your project’s North Star, preventing costly mistakes and rework down the road.
What’s the real difference between ‘Software as a Medical Device’ (SaMD) and a regular wellness app?
The line between these two is drawn by one simple concept: intended use. A wellness app is for general health tracking, like counting your steps or logging calories for fitness goals. It doesn’t make medical claims.
SaMD, on the other hand, is software specifically intended to diagnose, treat, prevent, or mitigate a disease. For instance, an application that analyzes MRI scans to flag potential tumors is squarely in SaMD territory. This medical purpose places it under the strict authority of regulators like the FDA. As a result, SaMD requires formal product engineering services that include a Quality Management System (QMS) aligned with ISO 13485, rigorous clinical validation, a thorough risk management file (ISO 14971), and ongoing post-market surveillance.
Can we use cloud platforms like AWS or Azure and still be HIPAA compliant?
Absolutely, but it’s not a “set it and forget it” situation. Major cloud providers like Amazon Web Services (AWS) and Microsoft Azure work on a ‘shared responsibility model.’ They secure the foundational cloud infrastructure: the physical data centers, the servers, the core network, but you are entirely responsible for securing everything you build on top of it.
To get started, you must sign a Business Associate Agreement (BAA) with your cloud provider. From there, it’s on you to correctly configure every service for encryption, strict access controls, audit logging, and data backups. Implementing strong cyber compliance solutions is non-negotiable to ensure your cloud architecture is truly secure and compliant.
What is ‘compliance-by-design’ and why is it important for healthcare software?
Compliance-by-design is a proactive approach where regulatory requirements are integrated into every stage of the software development lifecycle, from initial concept to post-launch maintenance. Instead of treating compliance as a final checklist before release, you build it into the DNA of the product. This is crucial for healthcare software because it reduces the risk of costly rework, speeds up time-to-market, and builds a fundamentally more secure and trustworthy product. It often requires a cultural shift, supported by digital transformation consulting, to become truly effective.
Ready to build a healthcare solution that’s secure, compliant, and built for the future? Bridge Global brings the expertise you need to cut through the regulatory noise and make compliance a genuine advantage. Let’s work together on your next custom healthcare software development project.