The Ultimate Guide to Scaling Healthcare SaaS Products
Growth creates a strange kind of stress in healthcare SaaS. The product is working, new customers are coming in, and the team finally has proof that the market cares. Then the second-order problems arrive. Response times start drifting. Integration requests pile up. Security reviews get longer. A rollout that felt manageable with a handful of customers starts breaking under real operational complexity.
That’s where many healthtech teams get stuck. They treat scale as an infrastructure problem and miss the bigger picture. In practice, scaling healthcare SaaS products is a coordination problem across architecture, compliance, implementation, support, and team design. If one layer lags, the whole system slows down.
The opportunity is large enough that getting this right matters. The global Healthcare SaaS market is projected to reach USD 167 billion by 2032 at a 17.58% CAGR, with over 90,000 healthcare organizations expected to adopt SaaS by 2025, according to Healthcare SaaS market projections. That kind of expansion rewards platforms that can scale without becoming brittle.
A lot of teams also learn that “working product” and “scalable company” are two different things. You need architecture that can absorb demand, delivery processes that don’t collapse under audit pressure, and a realistic plan for adoption inside hospitals, clinics, and multi-stakeholder care environments.
If you’re at that point, a capable healthtech software development partner can help close gaps faster. But the core work is still about judgment. What should stay simple, what needs to be rebuilt, and what must be standardized before growth turns into operational drag.
Your SaaS is Growing, Now What?
The first version of a healthcare SaaS product usually succeeds because it solves one painful problem well. It might streamline scheduling, centralize patient communication, surface analytics, or reduce manual work around care delivery. Early customers forgive rough edges if the product removes enough friction.
That tolerance fades as growth kicks in.
Larger customers bring procurement, security questionnaires, integration demands, and multiple user groups who all judge value differently. Clinicians care about workflow fit. Administrators care about efficiency. IT teams care about security, identity, uptime, and data exchange. Executives care about whether the platform can scale across sites without becoming another operational burden.
What changes when growth becomes real
At this stage, the product has to do more than function. It has to hold up under pressure.
A few signals usually show up together:
- Usage gets less predictable. One customer onboarded a department. Another wants an enterprise rollout.
- Feature velocity slows. Engineers spend more time stabilizing old decisions than shipping new work.
- Customer onboarding becomes uneven. Some accounts launch smoothly. Others stall on integration or change management.
- Compliance work expands. Security and privacy reviews stop being occasional hurdles and become part of the sales motion.
Growth in healthcare exposes weak assumptions faster than in most SaaS categories, because every failure lands inside a workflow people already consider high risk.
The mistake I see most often is treating these issues in isolation. Teams respond with a bigger cloud bill, more tickets, or a rushed refactor. That rarely fixes the root problem. The product needs a scaling model, not a patchwork of emergency responses.
The mindset shift that helps
Healthy scale in healthcare comes from three moves made together:
- Stabilize the platform foundation
- Reduce adoption friction for every stakeholder
- Build delivery systems that can keep quality high as complexity rises
That sounds obvious, but it's common to overweight one area. Strong engineering without implementation discipline still creates churn. Strong compliance without a flexible architecture slows delivery to a crawl. Fast product shipping without data interoperability creates customer frustration you can’t smooth over with better support.
That’s why scaling healthcare SaaS products has to be approached as an integrated operating model, not a single technical initiative.
Building a Foundation for Scalable Growth
Before changing architecture, I’d test whether the business is ready to scale. A surprising number of teams have a growth problem that looks technical but starts in product clarity, onboarding, or team structure.
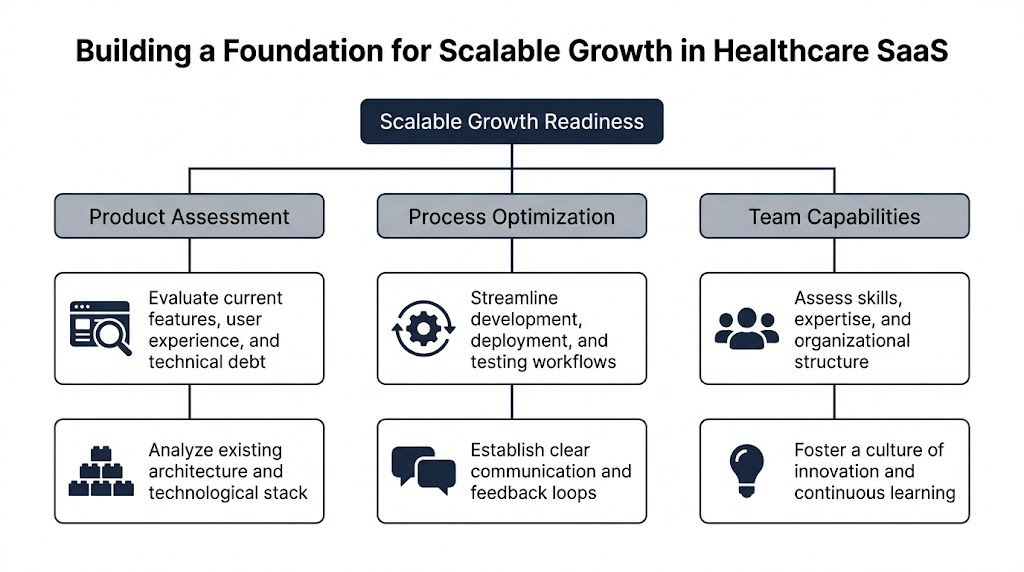
Healthcare SaaS has a specific penalty for weak implementation. Monthly churn can hover near 3.5% when onboarding and value delivery are poor, and clinician workflow disruption is a major reason adoption stalls, as noted in this analysis of healthtech SaaS adoption friction. That’s why foundation work has to include product, process, and implementation discipline, not just infrastructure.
Start with a readiness audit
Run a blunt assessment in four areas.
- Product fit under operational stress. Does the product solve one problem brilliantly, or several problems inconsistently? Scaling a muddled product multiplies support overhead.
- Implementation repeatability. Can your team onboard a new customer using a clear playbook, or does every account trigger custom decisions?
- Architecture health. Which parts of the system fail independently, and which failures cascade? If you can’t answer quickly, observability is already behind.
- Team ownership. Does each core domain have a clear owner across product, engineering, QA, and support?
A readiness audit should produce decisions, not a slide deck. Which workflows must be standardized? Which customers require configuration boundaries? Which legacy shortcuts are now blocking release speed?
Choose your tenancy model deliberately
Multi-tenancy decisions shape cost, performance, security posture, and support burden for years. Teams often default to a pooled model because it looks efficient early on. Sometimes that’s correct. Sometimes it creates painful exceptions later.
Here’s the practical trade-off:
| Tenancy model | Works well when | Main benefit | Main cost |
|---|---|---|---|
| Pooled | Customers share similar compliance and configuration needs | Lower operational overhead | Harder isolation and customer-specific exceptions |
| Siloed | Customers require stronger isolation or unique controls | Clear security and operational boundaries | Higher infrastructure and maintenance overhead |
| Hybrid | You need shared services with selective isolation | Balanced flexibility | More architectural complexity |
I generally recommend deciding tenancy by risk profile and operational reality, not by elegance. If enterprise customers expect stronger separation, pretending a pure pooled model will satisfy everyone usually creates rework. If smaller customers need speed and price efficiency, a fully siloed model can become expensive and slow to operate.
Practical rule: Pick the simplest tenancy model that satisfies your highest-likelihood customer segment, not the most demanding edge case on your roadmap.
Build compliance into the architecture
Healthcare teams lose time when they bolt compliance on after the product already has traction. By then, every shortcut is expensive. Access control is inconsistent. Audit trails are partial. Data retention rules vary by service. Logging captures too much in one area and too little in another.
A compliant-by-design approach usually includes:
- Role-based and context-aware access that matches real user responsibilities
- Auditability at service and data-event level so security reviews don’t turn into archaeology
- Encryption standards applied consistently across data at rest and in transit
- Environment separation for development, staging, and production with disciplined access policies
- Backup and recovery policies tied to actual operational risk
For teams working through those requirements, our guide on HIPAA compliant software development is a useful companion to architecture planning.
Reduce workflow disruption before it becomes churn
The product may be technically sound and still fail to scale because users resist it. In healthcare, that resistance is often rational. Clinicians don’t want another tool that adds clicks, creates duplicate entry, or breaks familiar workflows.
What works better is staged adoption.
- Pilot with a narrow use case that proves value inside an existing workflow.
- Train by role, not with one generic session for everyone.
- Measure implementation friction. Where do users hesitate, ask for workarounds, or revert to old processes?
- Expand only after value is visible to clinical, operational, and IT stakeholders.
A big-bang rollout looks faster in a roadmap. In reality, it often amplifies distrust.
If your engineering team is moving toward service decomposition, this practical guide on how to scale microservices is worth reading alongside healthcare-specific architecture decisions. The microservices pattern helps, but only when the surrounding release, ownership, and observability model is mature enough to support it.
Mastering Data Interoperability and Security
Healthcare products don’t scale cleanly if they act like islands. Customers want your application to fit into existing clinical and operational systems, not force a parallel workflow. That makes interoperability a product capability, not a side integration task.

The most common mistake here is building integrations one customer at a time without a durable data model behind them. You end up with brittle connectors, field-mapping logic scattered across services, and onboarding cycles that depend on a few engineers who know where the bodies are buried.
Interoperability has to be productized
If your platform touches patient data, scheduling, orders, clinical notes, billing context, or population health workflows, you need a consistent strategy for standards such as FHIR and HL7. Not because standards magically simplify healthcare data. They don’t. But they give your product a stable language for exchange.
A workable interoperability layer usually includes:
- Canonical internal data models so external system quirks don’t leak into every service
- Dedicated mapping and transformation logic instead of embedding translation rules all over the codebase
- Version-aware interface handling because upstream systems rarely change on your schedule
- Clear failure handling when external messages arrive incomplete, malformed, or delayed
Teams that skip this discipline often pay twice. First in slow implementations. Then in security and audit headaches, because nobody can easily explain how data moved through the system.
For a deeper look at healthcare exchange patterns, our guide on FHIR integration is a practical reference.
Security and interoperability are the same design conversation
A lot of teams separate these topics. That’s a mistake. The moment you enable data exchange, you expand your attack surface, your access-control matrix, and your audit obligations.
I like to evaluate security controls in the same workflow context as data movement. Ask four questions for every integration point:
| Control area | What to ask |
|---|---|
| Authentication | Which system or user is initiating the exchange? |
| Authorization | What data should that actor access, update, or trigger? |
| Audit trail | Can you reconstruct what happened without manual digging? |
| Data handling | Where is data stored, transformed, cached, and deleted? |
That forces practical decisions. Should a service cache PHI? Should support staff be able to view raw payloads? Should retries replay the entire event or only an encrypted reference? Those are architecture choices with compliance consequences.
Strong security in healthcare SaaS doesn’t come from one security feature. It comes from limiting ambiguity in how data is accessed, exchanged, and traced.
What mature controls actually look like
At scale, the basics still matter most. Not because they’re simple, but because teams often implement them unevenly.
Use this checklist as a working baseline:
- Access control discipline. Enforce least-privilege access for engineers, support staff, admins, and customer users.
- Encryption consistency. Don’t leave exceptions in logs, temp storage, exports, or message queues.
- Audit logging with reviewability. Logging everything is not enough if nobody can query or interpret it quickly.
- Data residency awareness. If you serve multiple markets, be explicit about where data lives and how it moves.
- Vendor scrutiny. Hosting, observability, support, and analytics vendors all affect your compliance posture.
When teams evaluate infrastructure options, this roundup of HIPAA compliant hosting providers can help frame the hosting side of the decision. Hosting alone won’t make an application compliant, but weak hosting choices can complicate everything else.
Trust shows up in sales, onboarding, and retention
Security work isn’t only defensive. It shortens diligence cycles when done well and documented clearly. Customers trust platforms that can answer hard questions fast. They also trust products that exchange data cleanly without creating operational surprises.
That’s where thoughtful cyber compliance solutions and disciplined custom healthcare software development become commercially useful, not just technically correct. If you want examples of how healthcare platforms solve those problems in real delivery settings, reviewing relevant client cases is often more instructive than reading generic compliance checklists.
Engineering for Performance and Reliability at Scale
Some healthcare SaaS teams keep a monolith too long because they’re afraid of distributed complexity. Others break everything into microservices too early and create a support nightmare. Both paths can fail.
The right question isn’t “monolith or microservices?” It’s “where does independent scaling or deployment materially reduce risk, delay, or cost?”

For healthcare SaaS, microservices architecture with cloud-based auto-scaling is critical because it supports independent service updates, more granular security controls for HIPAA, and dynamic resource adjustment for variable patient loads without unnecessary infrastructure spend, according to this healthcare SaaS engineering analysis.
When decomposition is worth it
I’d separate services when at least one of these is true:
- Different load patterns exist. Telehealth, document generation, analytics, and patient messaging rarely scale the same way.
- Release cadence differs sharply. A stable records service and a fast-moving workflow service shouldn’t always ship together.
- Security boundaries need tightening. Sensitive capabilities often benefit from clearer service-level isolation.
- Failure blast radius is too large. If one queue backlog slows the whole application, decomposition may be justified.
If none of those conditions are true, keep the architecture simpler. A modular monolith with strict boundaries can serve a growing healthcare product well for longer than many teams admit.
Reliability needs observability, not optimism
Scaling healthcare SaaS products without strong observability is mostly guesswork. Teams think they know why response times spiked or why a workflow failed. Then they spend hours correlating logs manually while customers wait.
A usable observability stack should answer three questions quickly:
- What is failing right now?
- Who is affected?
- What changed before the failure appeared?
That usually means instrumenting metrics, logs, and traces together, then aligning them with customer-facing workflows rather than just infrastructure components.
Here’s a practical operating view:
| Engineering concern | What to instrument |
|---|---|
| Latency | API response times, queue delays, database hotspots |
| Reliability | Error rates, retry storms, dependency failures |
| Capacity | CPU, memory, concurrency, connection saturation |
| User impact | Failed sign-ins, export delays, integration backlogs |
Don’t build alerts around every technical event. Build alerts around conditions that threaten customer workflows.
Auto-scaling helps, but it doesn’t excuse bad design
Cloud auto-scaling is valuable. It smooths variable demand and protects performance during spikes. It also hides poor resource usage if you’re not careful.
I’ve seen teams scale around avoidable issues such as:
- expensive database queries
- chatty internal APIs
- synchronous operations that should have been queued
- oversized payloads moving through services that didn’t need full records
- background jobs competing with user-facing traffic
That’s why performance work has to combine infrastructure controls with application discipline. Caching, asynchronous processing, load balancing, and distributed servers are useful, but they work best when the application model is already sane.
Release speed only matters if it stays safe
Healthcare teams can’t afford a release process built on heroics. If every deployment needs senior engineers on standby and a Slack war room, scale will slow product development long before the market does.
A strong delivery pipeline usually includes:
- Automated testing across critical workflows
- Environment parity as much as practical
- Progressive rollout patterns
- Rollback mechanisms that are tested, not assumed
- Change visibility for support and customer teams
Disciplined product engineering services can add structure, especially for teams modernizing architecture while still serving live customers. Ongoing reliability also depends on a realistic support model, which is why a mature plan for software maintenance and support should sit alongside engineering roadmap discussions instead of after them.
Integrating Intelligence and Scaling Your Operations
A healthcare SaaS company can reach the point where infrastructure is stable, releases are controlled, and growth still starts to drag. The bottleneck is often operational load. Implementation work piles up. QA cycles stretch. Support teams spend too much time classifying issues by hand. Engineering loses time on repetitive work that does not improve the product.
AI can reduce that drag if it is treated as an operating tool first and a product feature second.
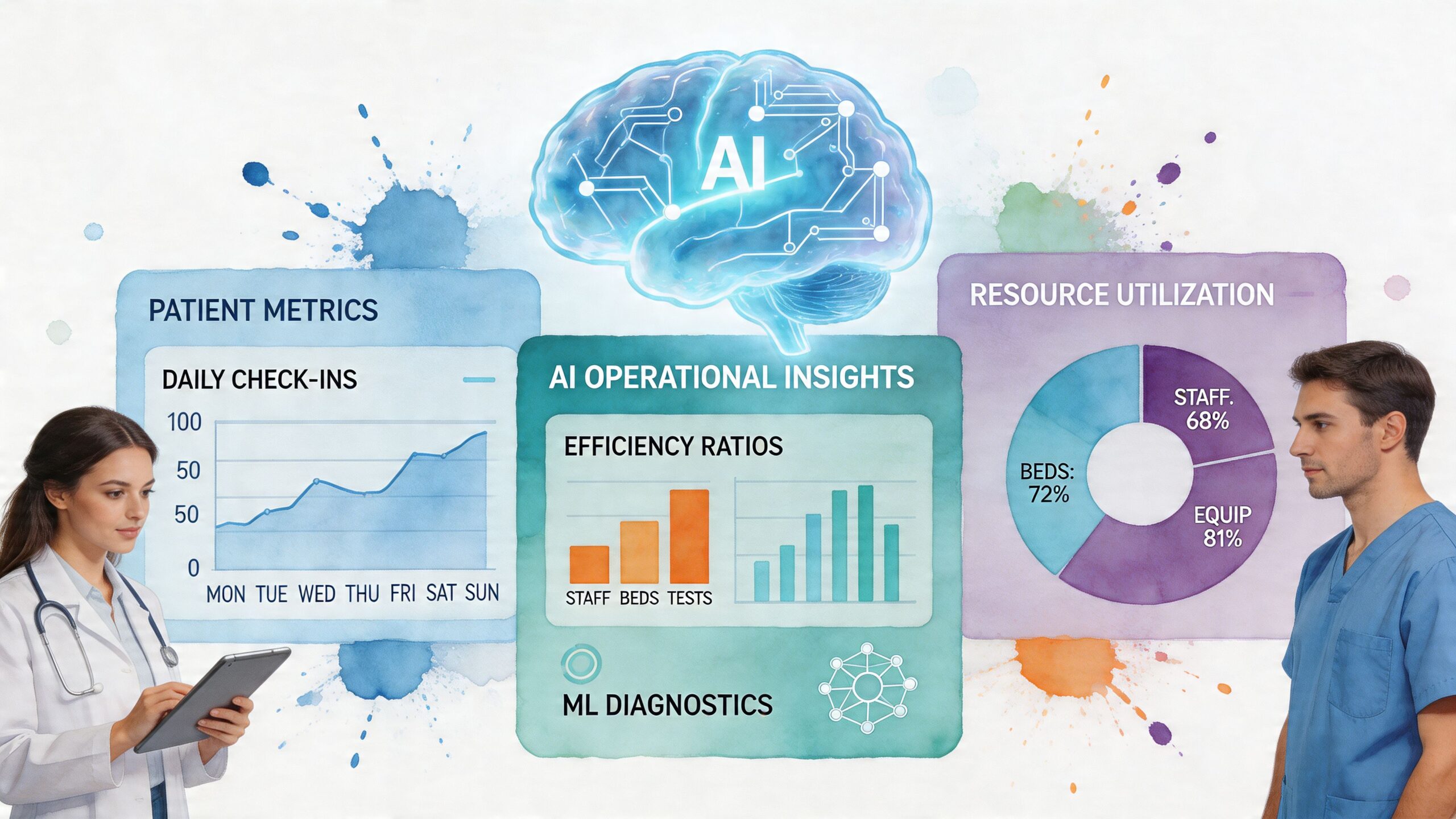
The practical win is not flashy. It comes from shortening work that experienced teams already know is expensive: mapping data fields during onboarding, generating first-pass test cases, summarizing support tickets, identifying failure patterns in logs, and drafting internal documentation that engineers can review instead of writing from scratch. In healthcare, that matters because compliance overhead and integration complexity already slow delivery. Teams that use AI well create margin in the process, not just novelty in the roadmap.
I have seen the strongest results in four areas:
- Implementation acceleration. AI helps teams prepare interface mappings, migration checklists, and draft transformation logic that engineers validate before production use.
- QA support. It can generate edge-case scenarios, expand regression coverage, and help teams spot workflow gaps in regulated paths.
- Operational triage. Support and engineering teams can classify incidents faster, summarize recurring ticket themes, and reduce time spent reading raw logs.
- Product intelligence. AI can support summarization, prioritization, anomaly detection, and prediction inside the product, but only where governance and review are defined upfront.
The order matters. Start with internal efficiency. Add customer-facing intelligence after the team has clear controls for data handling, model behavior, review, and auditability.
Healthcare buyers have good reason to be skeptical of vague AI claims. If a feature affects clinical decisions, billing outcomes, patient communication, or compliance-sensitive workflows, human review, traceability, and policy guardrails need to be designed into the workflow from the start. Teams that skip that step usually create rework for legal, security, customer success, and engineering all at once.
The same principle applies to team structure. Product complexity increases faster than headcount plans suggest. A team that could ship a narrow workflow with generalists starts to break down once the platform supports integrations, compliance operations, analytics, onboarding, and AI-assisted features at the same time.
Small cross-functional pods with clear domain ownership tend to hold up well under that pressure.
| Pod focus | Typical responsibility |
|---|---|
| Core platform | Identity, permissions, auditability, shared services |
| Clinical workflow | Day-to-day user experience and care-related flows |
| Integrations | EHR, HL7, FHIR, third-party data exchange |
| Data and intelligence | Reporting, analytics, AI-assisted capabilities |
That model works because ownership is explicit. Teams can move faster inside their domain, while shared standards for security, release control, and architecture stay centralized.
Hiring adds capacity only if the system around the team is already clear. Otherwise, each new engineer inherits tribal knowledge, creates another interpretation of “done,” and increases coordination cost. Before scaling headcount, document the decisions and operating rules that keep regulated software predictable:
- Architecture decision records
- Definition of done for regulated workflows
- Escalation paths for production issues
- Reusable onboarding playbooks
- Ownership boundaries between product, engineering, implementation, and support
After that foundation is in place, external capacity can help. A dedicated development team can add execution bandwidth when internal leaders want tighter delivery without splitting accountability across too many vendors.
For organizations formalizing AI use across engineering and operations, an ai transformation framework can help sequence use cases by risk and expected return. If the need is broader delivery support across architecture, build, and modernization, custom software development and targeted AI development services are relevant options. Bridge Global is one example of a firm that provides AI-driven software delivery and healthcare-focused implementation support as part of broader modernization work.
Your Roadmap to a Future-Ready Healthcare Platform
You sign three new health system customers in one quarter. Revenue looks good. Then the true test starts. One customer needs cleaner implementation handoffs, another exposes weak product boundaries, and the third pushes your reporting, audit trails, and support model harder than expected.
That is what scale looks like in healthcare SaaS. It is not a pure infrastructure problem. It is a coordination problem across architecture, compliance, delivery, and operations.
A future-ready platform is built by making a few disciplined choices early, then revisiting them as the business changes. Pick the parts of the product that must stay standard, and protect them. Isolate the places where customer variation is acceptable, and price that work correctly. Use AI in engineering and operations where it shortens low-value work, improves consistency, or helps teams ship regulated software with less manual drag. Build team processes that keep quality stable as headcount, customers, and integration load rise.
The trade-offs are rarely clean. A more configurable platform can help sales, but it can also increase test scope, validation effort, and support burden. Tighter standardization improves margins and delivery speed, but it may force harder commercial conversations. Microservices can reduce blast radius in the right domains, but they also add operational overhead and require stronger ownership. Good leaders make these calls with both gross margin and implementation reality in view.
The companies that scale well treat the product, the delivery model, and the operating system of the team as one strategy. They do not let compliance sit in a separate lane from architecture. They do not treat AI as a side experiment. They do not hire ahead of process maturity and hope structure appears later.
If leadership needs outside support, the useful kind is practical. It helps teams decide what to standardize now, what to automate next, and which constraints are worth accepting until the market, product, and delivery motion are ready for the next step.
Frequently Asked Questions about Scaling Healthcare SaaS
When should a healthcare SaaS company move from a monolith to microservices
Move when independent scaling, deployment, or security boundaries clearly matter. If one area of the product experiences very different demand patterns, changes more often than the rest of the system, or creates too much failure blast radius, decomposition may help. If the main pain is unclear ownership or weak testing, microservices usually won’t fix it.
What usually breaks first as healthcare SaaS usage grows
Implementation consistency often breaks before infrastructure. Teams can keep the app online while customer onboarding becomes slower, support volume climbs, and integration work turns into one-off custom engineering. In healthcare, that hurts adoption fast because users already have limited tolerance for workflow disruption.
How do you reduce adoption friction with clinicians
Start with narrow pilots inside real workflows. Train users by role. Remove duplicate entry wherever possible. Show clear value quickly. Clinicians rarely resist software because they dislike change in principle. They resist software that adds steps, interrupts patient care, or forces workarounds.
How important are FHIR and HL7 for scaling
They matter because customers expect your platform to exchange data without creating manual handoffs. The standards alone won’t solve interoperability, but they give your product a durable structure for integrating with EHRs and related systems. Key to this is building a clean internal data model and disciplined transformation layer.
What security controls should be in place before scaling upmarket
Have strong access controls, encryption, auditable user and system activity, backup and recovery procedures, and clear boundaries around where sensitive data is stored and processed. Also make sure your team can explain those controls clearly during diligence. Upmarket healthcare sales often slow down less because controls are missing and more because documentation is weak or inconsistent.
Can AI help early-stage healthcare SaaS teams scale responsibly
Yes, if it’s used selectively. AI is useful for speeding up development, testing, implementation prep, support triage, and analytics workflows. It’s less useful when teams force it into sensitive clinical experiences before governance is ready. Start with internal efficiency gains, then expand into product features that have clear guardrails.
When does it make sense to bring in an external partner
Bring in outside help when the team has reached a decision bottleneck, not just a staffing gap. Common triggers include stalled modernization, repeated compliance rework, slow release cycles, or implementation overload. A good partner helps create repeatable systems. They shouldn’t become the only people who understand how your platform works.
If you’re scaling a healthcare platform and need a practical partner for architecture, AI-enabled delivery, compliance-aware engineering, or team augmentation, Bridge Global works with product leaders and founders to turn growth-stage software into resilient, future-ready SaaS products.